Performance analysis of point multiplication algorithms in ECDH for an end-to-end VoIP network | Semantic Scholar
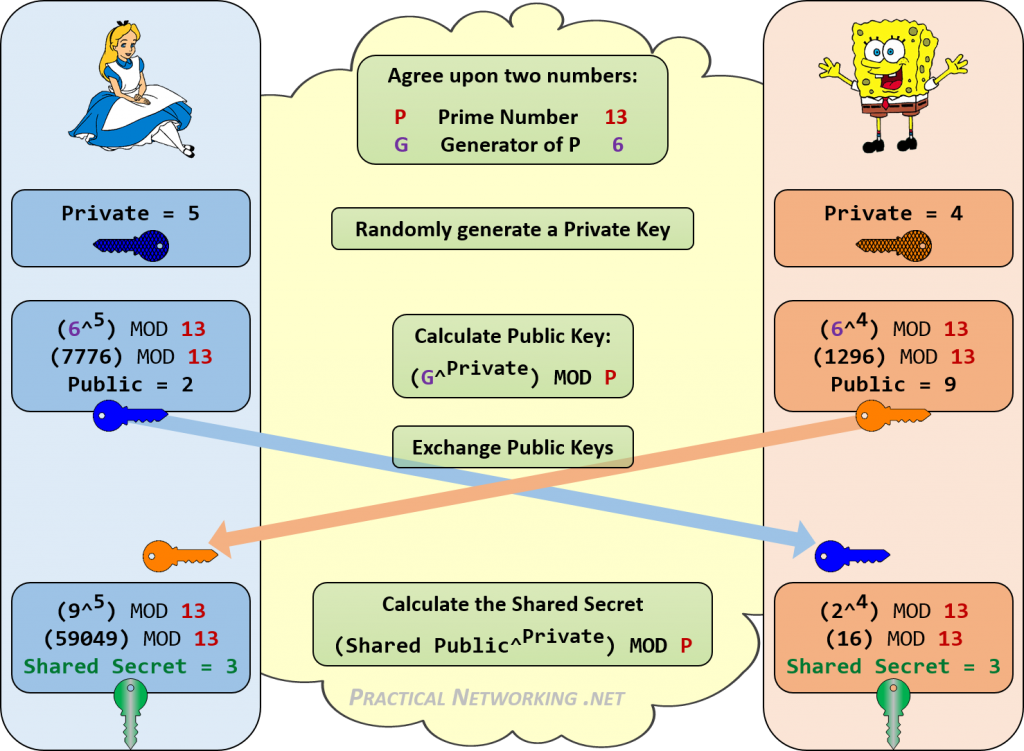
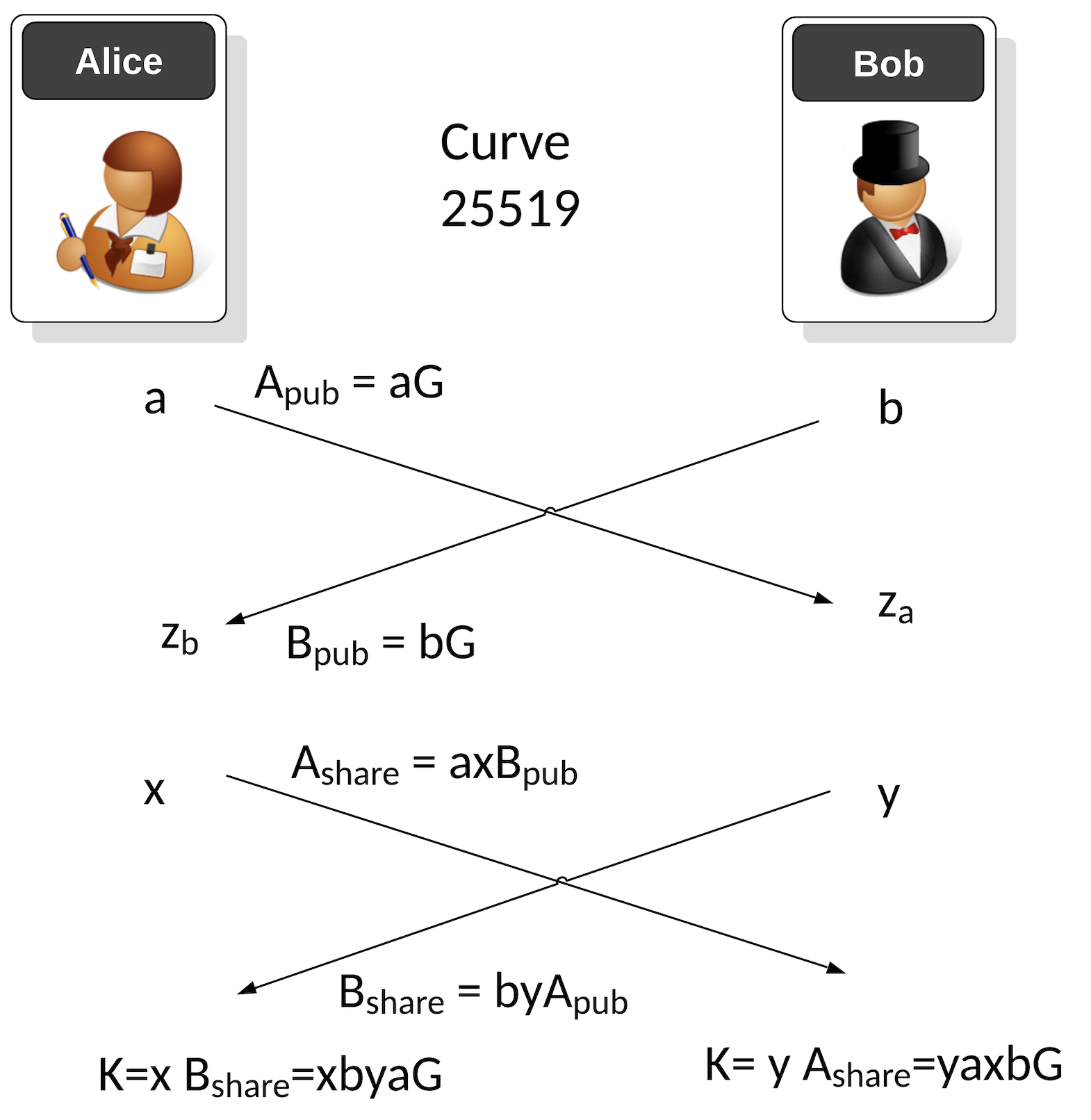
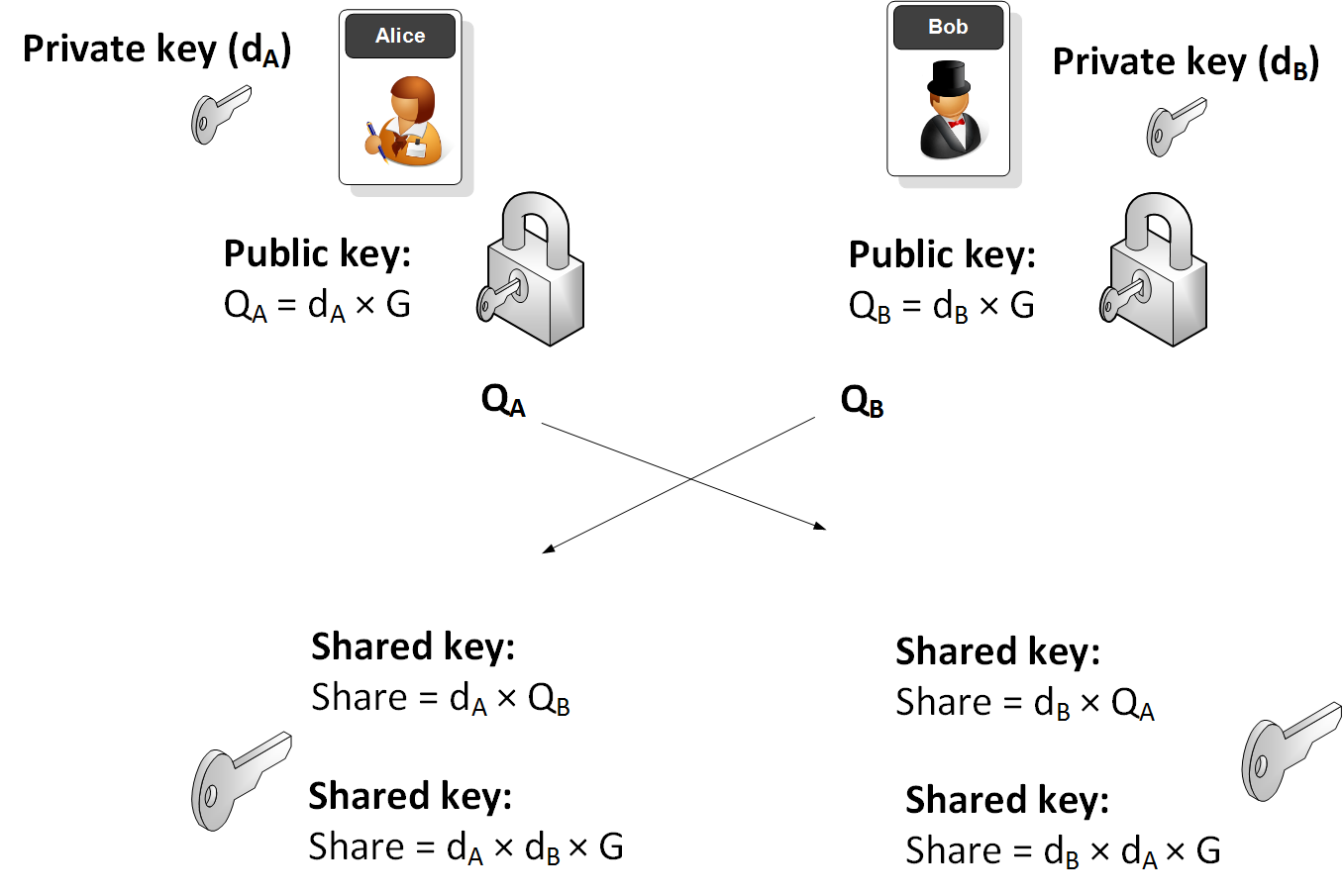
Implementing Elliptic-curve Diffie–Hellman Key Exchange Algorithm using C# (cross-platform) | David Tavarez

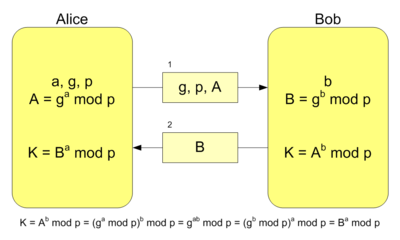
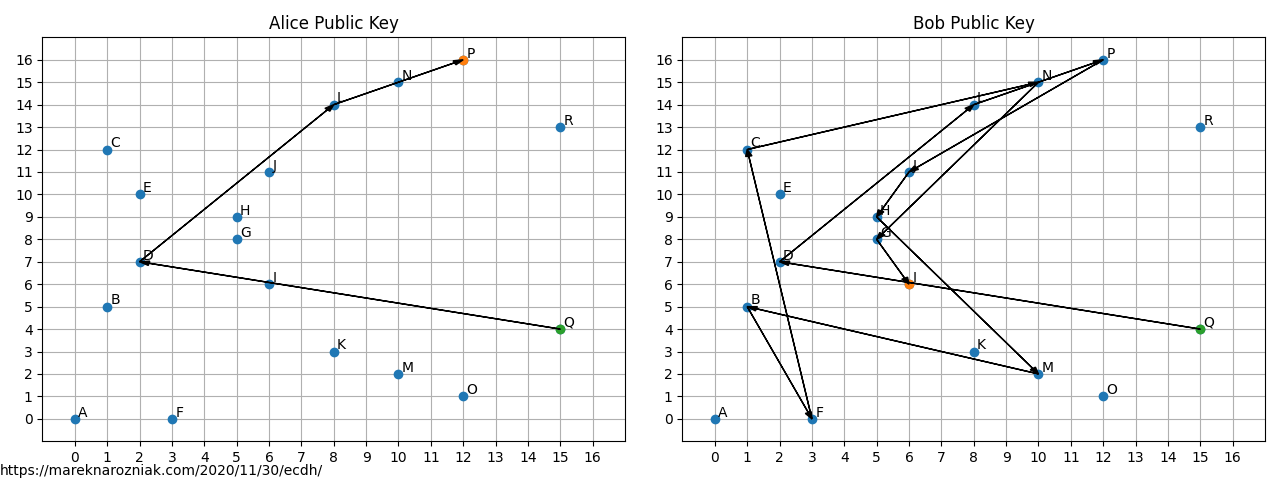
Figure 2 from Performance analysis of point multiplication algorithms in ECDH for an end-to-end VoIP network | Semantic Scholar

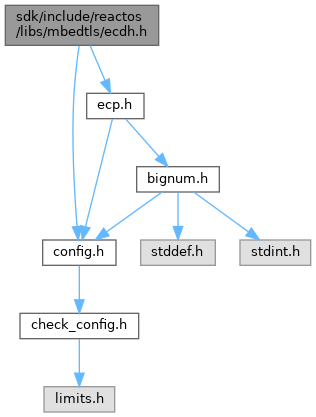
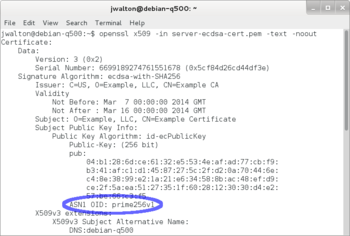
If We Were To Create the Internet again … it would be Tor-based | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium